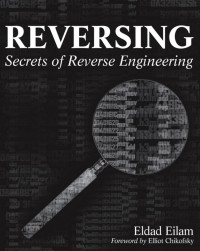
Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation
Bruce Dang, Alexandre Gazet, Elias Bachaalany, Sebastien Josse
Reverse engineering is the process of analyzing hardware or software and understanding it, without having access to the source code or design documents. Hackers are able to reverse engineer systems and exploit what they find with scary results. Now the good guys can use the same tools to thwart these threats. Practical Reverse Engineering goes under the hood of reverse engineering for security analysts, security engineers, and system programmers, so they can learn how to use these same processes to stop hackers in their tracks. The book covers x86, x64, and ARM (the first book to cover all three); Windows kernel-mode code rootkits and drivers; virtual machine protection techniques; and much more. Best of all, it offers a systematic approach to the material, with plenty of hands-on exercises and real-world examples.
年:
2014
出版社:
Wiley
语言:
english
页:
384
ISBN 10:
1118787315
ISBN 13:
9781118787311
文件:
PDF, 5.21 MB
IPFS:
,
english, 2014
 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  转换文件
转换文件 更多搜索结果
更多搜索结果 其他特权
其他特权